PyPI packages are increasing rapidly
PyPI is the main repository for Python packages. One thing that I've noticed recently is the number of published packages per week.
Let's look at published counts of new package versions per week:
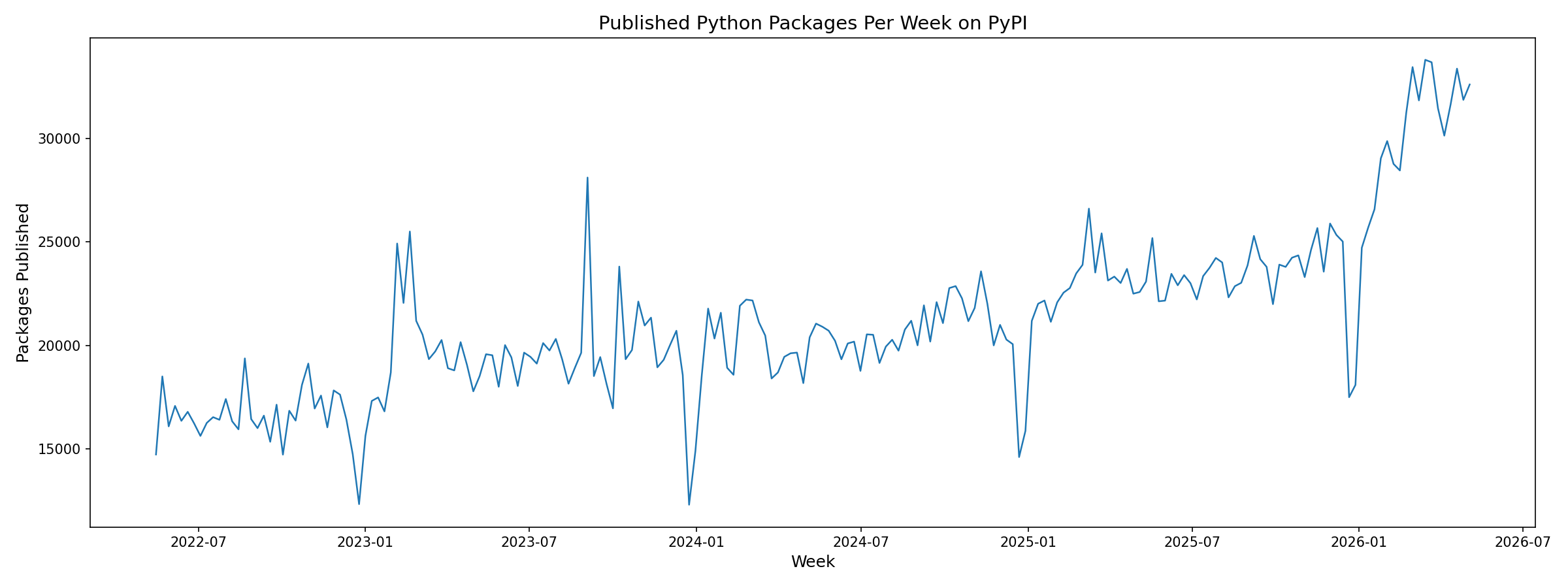
There are some dips in the data, but that's because of how the data was collected. We can see a clear increase in the number of published packages, especially in the last few months.
Because of AI, the number of packages published per week has increased by 30% since 2025.
I'm working on hexora, a library that detects malicious Python code in packages. It monitors newly published PyPI packages in real time and analyzes them.
A lot of packages, that have been published recently, are purely vibecoded, and they trigger false positive detections when my tool analyzes them.
For some reason, they abuse eval, exec, and subprocess where this can be entirely avoided.
In Python, eval and exec functions are used to execute code dynamically and are often used in malicious code to hide the payload.
The eval itself has a low signal and does not trigger detection. When sensitive data is passed to it, or the code looks like obfuscated, it's a red flag.
Sometimes, the code in such packages looks like malware. For example, one package reads Python code, modifies it as a string,
passes all environment variables and local variables to eval and executes it. This is rarely needed in projects.
If you really need to modify Python code, you can always modify AST trees instead.
Another project dumps Python code into a database as base64 encoded strings.
When retrieving the code from the database, it decodes and executes it with exec.
Why would you even encode it? Base64 manipulations only look malicious and do not compress the code in any way.
The code can be stored as a string!
And yes, a lot of them are related to LLMs: agentic frameworks, loops, and so on. That's one of the reasons they manipulate the code via exec/eval.
Increased amount of packages
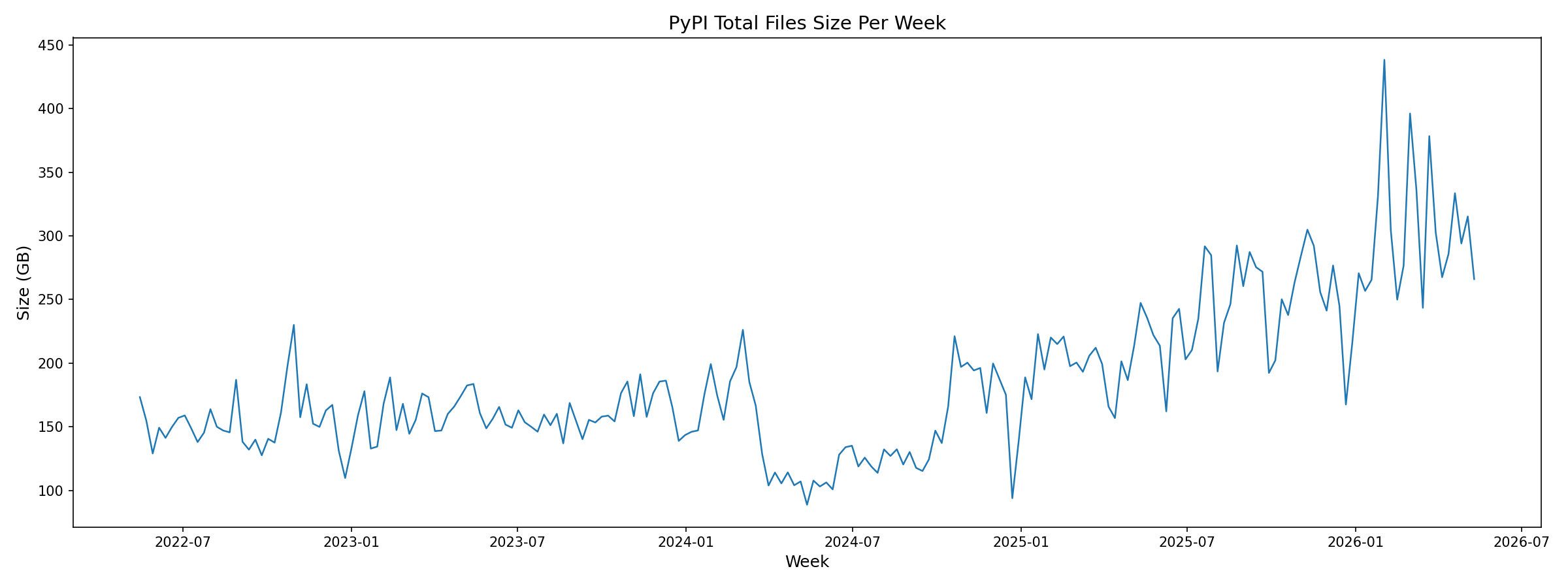
The growing number of packages and releases puts pressure on PyPI maintainers.
Storage requirement grows:
Weekly downloads also grow:
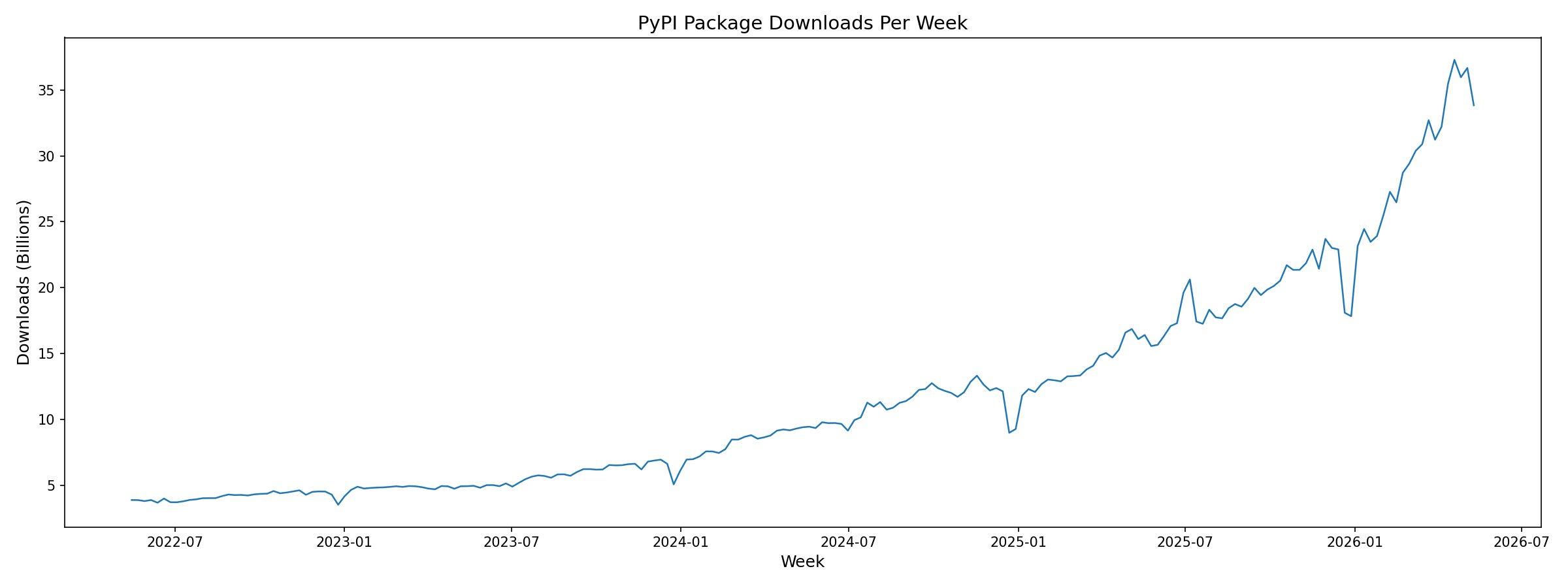
The PSF organization behind PyPI is a non-profit, and it relies on donations to cover costs.
Publishing frequency
While looking at the data, I've also noticed that some packages are published very frequently.
Why would you publish a package 392 times in a single day? That's an abusive behavior.
| name | day | published versions |
|---|---|---|
| esdd-client | 2026-03-04 | 392 |
| esdd-client | 2026-03-03 | 389 |
| muxi | 2026-01-07 | 251 |
| fray | 2026-03-18 | 229 |
| pymultirole-plugins | 2025-08-05 | 189 |
| wisent | 2025-12-30 | 186 |
| pyimporters-plugins | 2025-08-04 | 131 |
| djangodjangodjango | 2025-12-17 | 114 |
| pymultirole-plugins | 2025-08-04 | 110 |
| types-ibapi | 2026-02-11 | 110 |
| neurograd | 2025-09-14 | 95 |
| salmalm | 2026-02-23 | 92 |
| wisent | 2025-12-08 | 90 |
| authentik-client | 2025-09-13 | 89 |
| authentik-client | 2025-10-04 | 88 |
This trend is likely to continue, making it difficult to maintain the stability and security of the PyPI ecosystem. Projects that monitor supply chain attacks require manual intervention to filter false positives. The more packages are published, the greater the manual workload increases.
If you have any questions, feel free to ask them via e-mail displayed in the footer.
All articles on this website are written by a human.